
Have you ever worried about your website going down? Whether you run an online store or manage a blog, a downed site can mean lost traffic and business. While infrequent and short site outages are normal, some sites can go down for a much more malicious reason – a DDoS attack.
If you’ve ever been the target of a DDoS attack, or have witnessed one for yourself, you know exactly how debilitating it can be. But, what exactly is a DDoS attack, and how can you protect your website from it?
Let’s learn how DDoS attacks work to crash websites and the steps you can take to mitigate the damage.
What is a DDoS Attack?
A DDoS attack, short for Distributed Denial of Service, is an attack that overwhelms a server, network or service by overwhelming it with malicious traffic. A type of DoS (denial of service) attack, it floods the service, making it unavailable to legitimate user traffic. Many DDoS attacks utilize multiple devices, including computers and IoT (Internet of Things) devices, as sources of attack traffic.
How does an attacker gain access to that many devices? Typically, computers and devices used in DDoS attacks are infected with malware and exploited – this can either happen silently in the background of the device, or the malware can take total control. This group of devices is referred to as a botnet, which have also been responsible for ransomware, spam, and click fraud.
If this situation is hard to imagine, think of a traditional traffic jam on any street or highway that lead to your destination. A DDoS attack is similar to a highway being packed with a traffic jam of cars, blocking you or anyone else from getting onto the highway and to the place you’re trying to go. In this case, the destination is your website, and the traffic blocking people from moving is the DDoS attack.
So, clearly, a DDoS attack can be debilitating to a business. Preventing legitimate customers from accessing your site can cause huge losses. Let’s dive deeper into how DDoS attacks work and the different types that you should be aware of.
Common Types of DDoS Attacks
Before we learn about the most common types of DDoS attacks, we first need to gain a basic understanding of what they’re attacking – the network. Because network connectivity is a non-tangible concept, it’s usually described using the Open Systems Interconnection (OSI) model. This model conceptualizes network connectivity by dividing it into 7 layers, as shown below.
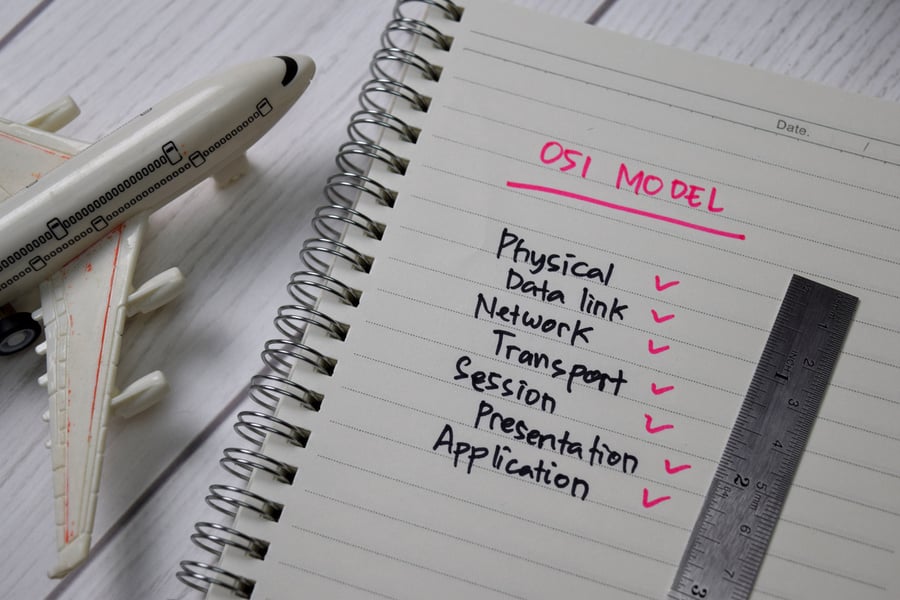
The most commonly targeted layers by DDoS attacks are the Network, Transport, Presentation, and Application layers. A DDoS attack targets specific layers to cripple connectivity at different points, preventing legitimate users from accessing your site.
Application Layer Attacks
As layer 7 DDoS attacks, application layer attacks targets the communication between users and a program or service. An application layer DDoS attack will focus on the part of network connectivity where the server generates web pages and delivers them in response to an HTTP request. Application layer attacks overwhelm servers by sending a large magnitude of malicious HTTP requests, which look legitimate and are hard to differentiate from real user traffic.
The two main types of application layer DDoS attacks are HTTP flood attacks. Both attacks overwhelm the target with HTTP requests, but they accomplish that in different ways.
HTTP GET floods involve multiple devices sending requests to a server for files, images, etc., which overwhelms the target server and leads to denial of service.
HTTP POST floods, rather than send requests for static content, send requests for dynamically generated resources like form submissions.
While flood attacks can be considered volume-based attacks, which we’ll get into later, application layer attacks typically follow a “low-and-slow” method. This means that they are smaller, easily slipping under the radar until they amplify and cause a service disruption.
Protocol Attacks
A protocol attack takes advantage of weaknesses on layers 3 and 4 of the OSI model. This type of DDoS attack sends more “packets”, or pieces of data, than your server is able to handle. Alternatively, a protocol attack can send an overwhelming amount of bandwidth to your network. Either way, this attack consumes your server’s resources and leads to a denial of service.
There are two major types of protocol attacks: SYN floods and Ping of Death (POD) attacks.
SYN floods take advantage of the TCP, which allows programs and devices to send each other messages. SYN is a type of TCP packet, which is sent to a device to request a connection. The device receiving that request will try to send a SYN-ACK response back. This attack exploits a weakness in this process, sending multiple SYN requests without responding to the SYN-ACK response. As the targeted device waits for that response acknowledgement, new connections can’t be made, and incoming requests are denied service.
Ping of Death, or POD, attacks take a different approach. Using a ping command, this DDoS attack sends multiple oversized packets to the target. A Ping of Death attack is able to send packets that are larger than the maximum packet size because it sends them as fragments. When the receiving server assembles all of the fragments, the data overflows and causes a denial of service.
Volume-Based Attacks
A volume-based DDoS attack works by taking up all available bandwidth between the target and all Internet traffic. It’s able to accomplish this by sending massive amounts of data to the target device through amplification. Volume-based attacks also frequently utilize botnets to take up bandwidth and deny service to the target.
Aside from HTTP floods, there are several other volume-based flood attacks that websites can fall victim to.
UDP floods send large amounts of User Datagram Protocol (UDP) data packets, taking advantage of the inherent weakness of UDP – it requires less checking than TCP would, letting traffic in easier. A UDP flood takes up host resources by sending these packets to random ports, which leads the host to repeatedly check and reply with an ICMP “Destination Unreachable” packet. Because of the amount of resources being held hostage by this attack, service can be denied to legitimate traffic.
ICMP floods work similarly, sending Internal Control Message Protocol (ICMP) request packets as quickly as possible to the target without giving it a chance to send a reply back. Because the server attempts to respond to all of the incoming packets, both outgoing and incoming bandwidth is being used. This can lead to denial of service for user traffic.
Why Do Websites Get DDoS Attacked?
The primary goal of a DDoS attack is to prevent legitimate user traffic from accessing your website, whether that’s by making the site slow or completely unreachable. However, the reason for someone to want to deny access to your website can vary. These are just a few reasons why a website can be DDoS attacked:
- Competition: A competing business may employ the use of a DDoS attack to try taking down the business they’re competing with. This can strategically coincide with big events, like a new product launch or a sale holiday like Cyber Monday.
- Hacktivism: Groups of “hacktivists”, which are political activists that use hacking as a tool, may use DDoS attacks to target websites that they ideologically oppose.
- Extortion: Online criminals can use DDoS attacks (or even simply a threat of attack) to extort money from the target website through ransom or blackmail.
- Vandalism: A DDoS attack can sometimes happen for no real reason – it could simply be because a cyber-vandal decided to attack a site for fun.
Whatever the reason for the attack, one thing is certain – a DDoS attack is not able to steal sensitive information from your website. Even still, being the victim of a DDoS attack can be devastating to your business.
What to Do If Your Website Is Being Attacked

Without prior preparation and protection, it can be difficult (and sometimes impossible) to outright stop a DDoS attack once it’s begun. However, if your website is currently being attacked, there are a few things that you can do to try and mitigate it.
1. Communicate with the right people in your organization.
The first step you need to take after a DDoS attack starts is to notify the people in your organization who can take action. This can include network administrators, stakeholders, community managers, and anyone else who needs to know what’s happening first. They should have preparations in place to begin mitigating what they can from your site’s side of things.
You may also want to communicate with customers letting them know that there is a situation, whether via email or social media channels.
2. Contact your ISP, web hosting provider, or security service.
Your next immediate step would be to notify all services involved in routing traffic to your site that you are experiencing a DDoS attack. From there, each service can attempt to mitigate the incoming malicious traffic.
Your ISP can use black hole routing, which directs traffic away from your site and into a “null route.” Web hosting providers may be able to assist in minimizing the impact of the attack by scaling up your service. Any security services that you have in place should have security tools dedicated to stopping DDoS attacks.
3. Start blocking traffic and limiting requests.
Next, either your network team or ISP should implement IP-based Access Control Lists, or ACLs, to block malicious traffic coming in from the attack source. In the case that your application or web-based service is being attacked, they may also implement rate limiting, which imposes a limit on concurrent application connections. However, because rate limiting can’t differentiate between legitimate traffic and malicious traffic, it may deny service to real users.
4. Monitor the attack and your defense.
Throughout the attack, it’s vital that you and your team monitor its progression. You should be able to gather what type of attack it was, how large it was, whether it was coming from one source or multiple, the location and identity of those sources, and the attack pattern used.
All of this information can be used after the attack to determine how your defenses worked to protect your site and any mishaps that can be corrected for future attacks. You’ll also want to take note of metrics, like “time to mitigate” and “consistency of mitigation” to see how quickly and effectively your ISP stopped the attack.
How to Prepare for DDoS Attacks
The best way to stop a DDoS attack is to prevent it from happening in the first place. To keep your site safe and operational, follow these steps for preparing for DDoS attacks.
1. Learn about your provider and host’s protections against DDoS attacks.
Your ISP and web host may already have security protections in place to guard against DDoS attacks. For example, leading content delivery network Cloudflare has comprehensive DDoS protection built-in. This includes web asset protection, a cloud-based Web Application Firewall, a reverse proxy service, BGP-based DDoS protection, and much more.
If your provider doesn’t come with DDoS protection services like these, you may want to look into switching providers or employing security on your own.
2. Create a plan for responding to DDoS attacks.
In case your site is ever the target of a DDoS attack, you need to have a plan in place to mitigate it as best as possible. First, comb through your system for any weaknesses or vulnerabilities – line out how you’ll be eliminating those issues. Then, define a clear response for your company. What is your process of identification, communication, and mitigation?
Finally, you’ll want to put together a dedicated response team who can take action. Keep network administrators, your IT department, and any other relevant department in the loop on what their responsibilities are in the event that you are attacked.
3. Use a Website Application Firewall (WAF).
A Website Application Firewall, usually shortened to WAF, is a type of firewall that monitors and filters traffic coming into your site. A WAF can identify and block requests from attackers while allowing legitimate traffic users to come through and visit your site. It identifies malicious requests by focusing on the data contained within the attempted transfer. If it finds that the traffic is malicious, it redirects it to other content delivery networks to distribute that load away from your site’s server.
Many content delivery networks, or CDNs, come with a WAF built in. Be sure to inquire about this when you contact your ISP and host.
4. Keep all systems and software up to date.
An out-of-date system can be especially vulnerable to DDoS attacks. Without the newest version of any software that you use, your site may not be fully protected. Like most cyber-attacks, DDoS attacks are constantly evolving as bad actors learn how to bypass defense systems. So, to keep your site well-protected, be sure to not miss out on any software updates.
Moving Forward
If you’ve been a victim of a DDoS attack, you’re not alone. Even major organizations like Amazon Web Services and GitHub have been victims of DDoS attacks, causing outages for users across the internet.
As an online business, any amount of downtime can feel like money going down the drain. But, with information and preparation on your side, you can protect your site and prevent it from affecting your business.





Leave a reply or comment below